Benefits of Outsourcing Marketing Services
In the business world, marketing can be a major factor in achieving a competitive edge. However, not every business can…
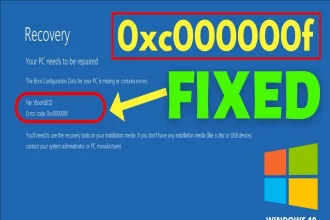
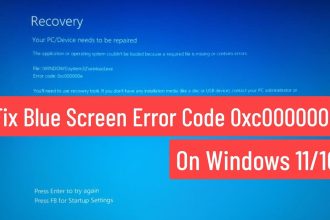
An Unidentified Error Occurred PS5 : How to Fix it
An Unidentified Error Occurred PS5 - How to Fix It : It is hard to pinpoint…
Education
View All